Understanding the Critical Role of a VPN in Modern Digital Life
In an era where digital vulnerabilities are growing, safeguarding your personal information has never been more essential. A VPN scrambles your digital communications, ensuring that hackers, network administrators, and unauthorized users cannot track your online behavior. Whether you’re accessing public Wi-Fi at a airport or processing confidential files, a VPN acts as an protective layer against security leaks.
Many users ignore the dangers of unprotected hotspots, leaving vulnerable their credit card numbers, passwords, and communication logs. By routing your connection through secure servers, a 快连 conceals your digital location and physical whereabouts, making it nearly unfeasible for tracking agencies to profile you.
Selecting the Ideal VPN for Your System: A Comprehensive Comparison
Selecting the right VPN solution relies on your unique requirements and OS. For Microsoft enthusiasts, look for easy navigation, fast servers, and rigorous encryption. MacOS devotees should prioritize flawless operation with iCloud services, while Linux aficionados may favor configurable options.
Smartphone users must select VPNs with compact software that limit energy usage and bandwidth usage. Multi-device support is critical if you regularly move between computers, slates, and devices. Always confirm that your VPN works with modern standards like OpenVPN for best results.
Step-by-Step Guide to Installing a VPN on PC Systems
Start by, access the provider’s portal using a trusted browser. Locate the download section and choose the PC-friendly edition. Once downloaded, execute the installer and follow the step-by-step instructions.
While configuring, adjust preferences like auto-connect and encryption choice. Enable the kill switch feature to prevent breaches if the VPN drops. Lastly, authenticate with your credentials and connect to a server of your choice.
Optimizing VPN Usage on MacOS
Apple’s platform delivers integrated features for VPNs, but external software often offer enhanced functionality. Post-installation, move the VPN software to your Applications folder. Launch the app and enter your subscription details to activate the service.
Adjust configurations such as security levels and node choices. Turn on traffic filtering to direct specific apps through the 快连电脑版 while letting others to use your regular connection. For added protection, integrate your VPN with Firewall tools to prevent spyware and scam websites.
Securing Tech-Advanced Devices with a VPN
Tech enthusiasts often favor VPNs that support command-line interfaces. Begin by, updating your system library to guarantee compatibility to the latest VPN software. Use CLI instructions to set up the VPN client, adhering to documentation provided by your provider.
Adjust network settings to simplify VPN sessions during system startup. Experienced individuals can integrate firewall rules to block insecure connections. Regularly audit reports to identify irregularities and upgrade your VPN software to resolve weaknesses.
Protecting Handheld Gadgets with VPNs on Android and Apple’s Platform
Handheld gadgets are prime targets for security incidents due to their always-online nature. Get your VPN app from the official marketplace to steer clear of fake apps. Open the app, sign in, and select a location nearby for faster speeds.
Enable tools including ad-blocking to improve your online sessions. Set up the VPN to auto-connect when accessing open hotspots. For iOS users, enable continuous protection in device settings to sustain security even if the app shuts down.
Advanced VPN Features to Enhance Your Protection check here
Today’s services deliver cutting-edge options that go beyond simple security. A emergency stop stops all internet traffic if the VPN drops, preventing leaks. Server chaining routes your connection through two or more locations, obscuring your internet footprint to a greater extent.
Ad and malware blockers remove malicious banners and halt phishing sites. Split tunneling lets you decide which apps use the VPN, balancing speed and security. For organizations, fixed locations and user management streamline protected teamwork.
Addressing Common Misconceptions About VPNs
Even with their widespread use, many users misunderstand how VPNs operate. A common fallacy is that VPNs completely make anonymous your online activity. While they hide your IP address, tracking cookies can still leak your identity. Additionally, few VPNs practice strict no-logs policies, so researching your provider’s practices is essential.
A further misconception is that VPNs dramatically reduce network performance. While data scrambling introduces overhead, top-tier tools minimize this impact with optimized servers. Lastly, free VPNs often sacrifice security by sharing user data or displaying intrusive ads.
Future-Proofing Your Online Presence with a VPN
As digital landscapes shift, remaining secure requires forward-thinking steps. Emerging trends like advanced algorithms could undermine current security protocols, making it crucial to opt for VPNs committed to improving their networks. Integrating a VPN with extra safeguards like secure storage and biometric checks establishes a comprehensive security strategy.
Governments worldwide are enhancing data privacy laws, and a VPN helps you adhere with these requirements. Whether you’re streaming content, gaming online, or handling professional tasks, a VPN is an indispensable tool for operating the internet landscape confidently.
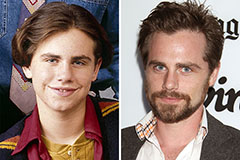 Rider Strong Then & Now!
Rider Strong Then & Now! Tahj Mowry Then & Now!
Tahj Mowry Then & Now!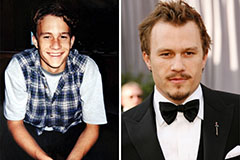 Heath Ledger Then & Now!
Heath Ledger Then & Now! Karyn Parsons Then & Now!
Karyn Parsons Then & Now! Tyra Banks Then & Now!
Tyra Banks Then & Now!